Shop
Showing 73–96 of 2153 results
-

A Tale of Two Cities
550 ৳ Add to cart -

A Tale of Two Cities Penguin Select
1000 ৳ Add to cart -

A Tale of Two Cities Singature Classics
2200 ৳ Add to cart -

A Taste For Death
1600 ৳ Add to cart -

A Thousand Splendid Suns
1200 ৳ Add to cart -

A Trail Through Time
1200 ৳ Add to cart -

A View From The Bridge
1400 ৳ Add to cart -
A Voyage to Arcturus
1400 ৳ Add to cart -

A Wild Sheep Chase
1200 ৳ Add to cart -

A World of Ice And Fire Illustraded Hardcover
4800 ৳ Add to cart -

A World of Three Zeroes
1200 ৳ Add to cart -

A World of Three Zeroes Hardcover
1800 ৳ Add to cart -

A World Without Email
1400 ৳ Add to cart -
Sale!
A Year To Change Your Mind
Original price was: 1800 ৳ .1600 ৳ Current price is: 1600 ৳ . Add to cart -
A Year With Rumi
2400 ৳ Add to cart -

Absent In The Spring
800 ৳ Add to cart -

Abu Bakr As Siddeeq
1800 ৳ Add to cart -
Accidentally Amy
1200 ৳ Add to cart -

ACOTAR Box Set (5 books)
6000 ৳ Add to cart -

Adulthood Rites
1600 ৳ Add to cart -
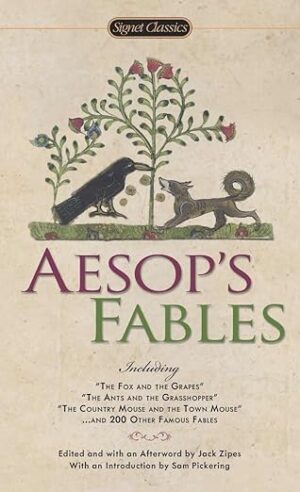
Aesop’s Fables
1100 ৳ Add to cart -

After Dark
1000 ৳ Add to cart -

After I Do Taylor Jenkins Reid
1100 ৳ Add to cart -

After The Darkness
1200 ৳ Add to cart
